The hacking of social media accounts is no longer fresh news. It’s now a question of “who’s account did hackers hack today?” News about hacking the social media accounts of top corporations is something that has flooded numerous front pages.
You’d be wondering if anybody’s accounts still get hacked? With various reports about hackers taking over accounts, you’d assume everyone is now more careful with their social media accounts.
Even in the most technologically advanced countries, you’d be surprised how easily people lose their social media accounts to hackers. These hackers adopt various means of stealing people’s account information. Hackers steal accounts for various purposes, including stealing your personal information or sending spam messages to your friends and followers.
This article is going to help you stay ahead of hackers. Keep reading, and we’ll provide practical information in this article that’ll help you stay many steps ahead of hackers and the approach they’ll use to try to steal any of your social media accounts.
How Hackers Get Hold Of People’s Social Media Accounts And What You Should Do
You’d be wondering how exactly people lose their accounts to hackers. If everyone has a unique username and password that’s supposed to be secure, how come hackers steal people’s accounts daily and seemingly easily?
Indeed, social media accounts have “unique and secure” login details associated with each user account. Holders of these unique login details often play a role in the successful theft of those login details and subsequent account loss. Education can go a long way in preventing these account thefts.
Some of the methods adopted by hackers include:
Phishing And Phishing Baits
Phishing scams are still the easiest way of stealing account information from users. Not minding how rampant it has become, hackers still use this method very often to try and take over ownership of people’s social media accounts.
Hackers can design a look-alike site of your popular social media to use them and steal information from you.
Phishing baits occur when these hackers contact you over the phone or through emails. Their message will normally encourage you to click a link. They’ll often tell you about some promotional offers that require you to fill in any of your social media login details for whatever purpose(s) they’ll state in their message.
An unsuspecting victim will readily fill in their details and submit them to the phishing site. Once the hacker has the login details to the social media site they want, they can quickly reset the user information.
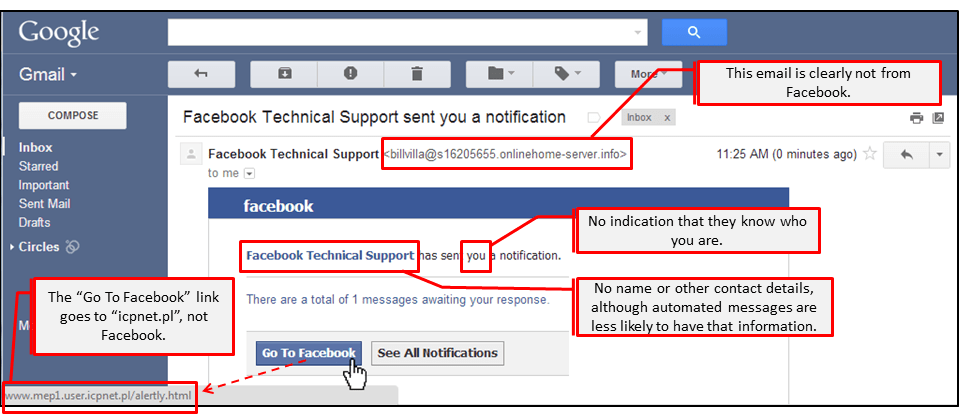
An image example of a phishing email, pointing out all the red flags.
What You Should Do
- Be careful about the messages you receive from unknown sources. Before you click any link in an email, ensure they’re links from sources you trust.
- Don’t always fill in your social media login details on sites you visited through links. Always type in the web address of your social media sites on your address bar.
Password Management
How you handle your account passwords could make all the difference. Who have you told your password(s) to your various social media account? Do you use the same password for all your accounts? Does your password still look something like “password?”
All these are vital to the security of your social media accounts. And even more vital is where you stick passwords to your social media accounts. Sticking your password in front of your computer screen might “help you remember” your password, but it also exposes those passwords to eyes looking over your shoulder.
How about saving your passwords on your computer? Even that isn’t safe. Anyone could gain access to your computer, and that’ll expose your login details to them.
What You Should Do
- Your passwords are personal and shouldn’t be shared with everyone. Keep them as private as possible.
- Don’t use your pet’s name or school year as your password. Easy to guess passwords are bad options. Your passwords should be a mixture of numbers, uppercase letters, and special characters. The longer, the better.
- Be careful how you expose your passwords. Instead of saving them in your system, password management tools could help you maintain them securely.
Cookies And Session Attack
Do you remember how you don’t have to enter your password to log in to your Facebook account? When you enter your password and log in today, your browser will never forget that you’ve logged in and not ask for your password tomorrow.
Your browser stores your login in a session and remembers you each time you open Facebook again on the same browser. Except you log out and destroy that session, your browser will never forget that you’ve logged in using your credentials.
An attack can be carried out against you using those stored sessions. If you use a free, insecure wife in a coffee shop, for instance, a hacker can intercept your login session and use that to steal your social media account information.
What You Should Do
- Be careful of the networks you’re using. Before you connect to any open network, ensure it’s safe for your use.
- Each time you complete whatever you’re doing on any of your social media accounts, log out. It’ll take you a little extra pain of logging back in each time you return to the site. But the security of your account could be worth that extra pain.
- Activate two-factor authentication for your social media account. It’s available on various social media platforms. Even when a hacker gets hold of your login credentials, they’ll not have access to your phone or email accounts.
Third-Party Applications And Softwares
While using your social media accounts, you may come across apps or software that’ll offer to help you do a thing or the other.
These are third-party apps, and the owners of your social media platforms are not in control of these apps. A hacker can easily build one, and when you install them, the hacker already has easy access to stealing your account.
What You Should Do
- Don’t just install any third-party app you come across. Ensure who the owner is and what those apps would do on your accounts.
- Finding out the originating country of the apps you install could be a valid way to determine if those apps are truly what they claim.
Conclusion
For the security of your social media accounts, you have to be conscious of how you handle those accounts. Each private account information is vital, and you must treat them as confidential.
Author Bio:
Sherri Carrier is a professional writer and an assignment writing services enthusiast. She is a member of several writing clubs in New York. Also, she has an artistic side to her as she loves poetry. She is inspired by her favorite writers and the people she loves.