It is essential to know how one becomes the victim of any cybersecurity threat so that you can safeguard yourself and protect your privacy. Let us consider a situation where suddenly your smartphone starts acting weird. To try out a solution, you contact your phone carrier but instead of figuring out your problem, they inform you that you are no longer on their customer list.
They further notify you that your mobile phone account has been transferred to another person’s carrier. Please be aware that this is the initial stage of cybercrime against you.
Now looking at it from a different viewpoint, there are multiple data breaches, ransomware, phishing attacks, and cybercrimes that are coming up rapidly and hampering the daily lives of the users. From the recent statistics, it is clear that not only are the cybercriminals trying to intrude into the users’ gadgets but also the CIA has been hacking smartphones for ages to snoop into the personal lives of people. They want to gather personal information.
Thus, it is very important to hack-proof your smartphone and take some important safety measures so that you can keep your data safe and secure. So, let us have a brief look over the 5 killer steps to hack-proof your smartphone.
1. Setting up a Pin in the mobile account of your smartphone carrier –
If you are willing to put a fruitful effort to prevent your mobile account from being hacked, then protecting and securing your account with a pin is the best idea. This step generally includes setting up a pin or passcode in the account with the help of the mobile carrier.

Once the pin is added to your account, you are technically freezing your account, so henceforth no changes or alterations can be made without your permission. That’s how you are restricting the hackers from acquiring your personal information and data.
Once you are asked for your pin regarding various events like logging into your account, calling your carrier, or visiting a physical store, you are enabled to set up the feature online or over your phone. But do remember to create an uncommon passcode.
2. Protecting and Securing Your Smartphone with a passcode –

According to a research study conducted by Symantec, it was observed that Symantec dispatched around 50 unprotected unsafe smartphones in the public region. However, as per the outcome, it was discovered that 89% of the people were searching for personal applications, 60% of the persons were searching for social media or email applications. Whereas 57% tried to open password files and 50% of them contacted the mobile-owner.
Thus the addition of a passcode on the device can be considered a simple choice. In comparison to a smartphone, generally in iPhones, there are multiple options like four-digit code, six-digit code, or even custom alphanumeric codes.
The six-digit or the alpha-numeric codes are much more secure and safe. iPhone also leaves open the option of touch ID as well as the choice of changing the passcode at any time.
In the case of androids, there are also multiple options like locking patterns, passcode digits, or even a password. The tech specialists state that passwords are more secured and protected than the lock screen patterns.
3. Activating the Feature of “Find My Phone” –
It is really fascinating to know that both Apple phones and Android devices have a special kind of in-built feature through which the user is enabled to track their lost phone, lock their device, turn off their phones and even erase all the personal data stored in the device. This is just an alternative to getting your lost phone back without the usage of any passcode whatsoever.
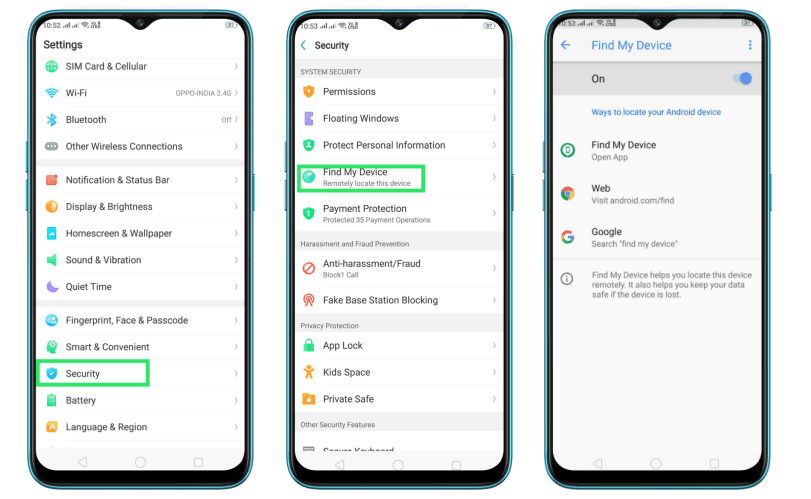
In cases of Apple phones, there is a pre-installed feature in the settings namely “Find my iPhone” and in cases of android devices, there is a feature called “Find My Device” in the google settings. Once you activate the location services for both these features, you can get back your lost phone with complete security.
4. Updating the software and applications of the smartphone when notified –
Most people feel reluctant towards updating the software and applications of their phones. It has been discovered that they feel an unknown fear of a new operating system alternating the phones’ previous interface. Also, they don’t want their messaging application to change. Thus the chances of closing up the gap of security vulnerabilities through various updates start to diminish, as well as the security risks tend to increase.
Alongshore the operating system, all the running applications are also required to be updated on a regular time interval so that the hackers don’t find any security breach through the outdated applications. It is also highly recommended that the applications must be downloaded from the official application stores for security and privacy reasons. This process generally excludes malware and threats.
5. Backing up the phone at a regular time interval –
Another way of following the safety measures and precautions is to back up your phone on a regular time interval in two places, which are respectively in your computer and in the cloud. Consider some sudden and unavoidable cases like you are attacked by malware or your phone is hacked then you can easily factory reset your phone which will erase all your data but you will be assured that they are safe somewhere else. Afterward, you can easily download all your data from the backup.
If you just connect your phone to your computer through a USB and follow the basic instructions, all your data will be backed up. In the case of iPhone users, if the device is plugged in, connected to the internet and the iCloud is enabled then automatically all your data will be backed up in the cloud.
In the case of Android users, they can easily link their phones to the google accounts and the backup will be automatically held through the settings.
Conclusion –
All these steps can be utilized to hack-proof or protect your smartphone. Simultaneously you can choose the level of cybersecurity and can upgrade according to that. You can choose selected actions from the above as the implementation of all these options will offer you the best security and protection.
Author Bio:
Name: Jainish Vora
Bio: Jainish Vora is Author at Phoneier. Having experience with 5 years of writing about phones and other gadgets. He loves to explore and write different gadgets from android phones to wearable gadgets.