There was a time when most people tended to consider blockchain to be highly prominent in the security department. However, then a 51% attack occurred and all hell broke loose.
But, what is it, though?
How does it work?
Why is blockchain so vulnerable against it?
In this article, we have answered all of these questions in an elaborate manner. So, hopefully, it will help you understand the titular topic properly. Let’s get started, then.
51% Attack – What Is It?
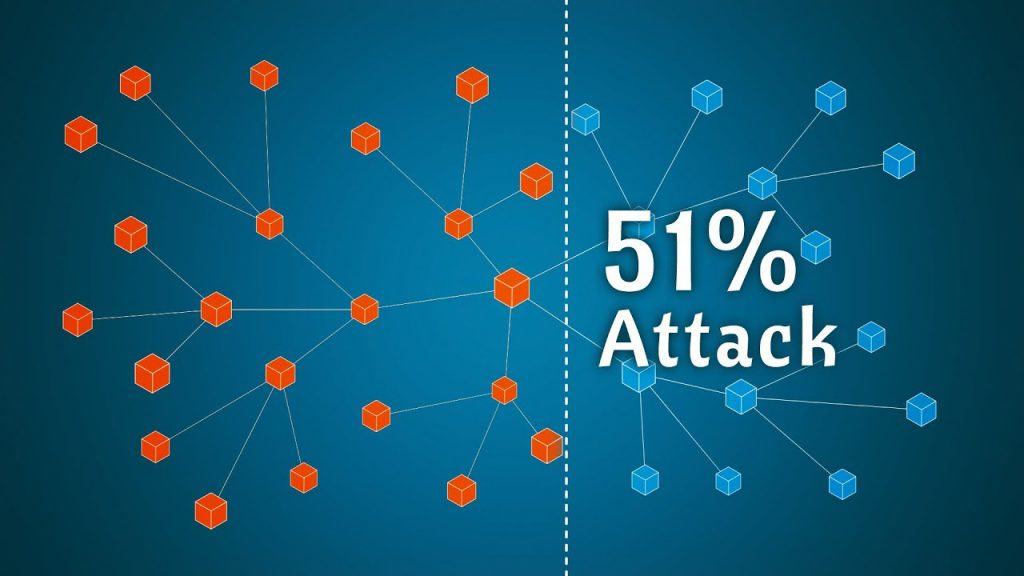
A 51% attack is a type of cybercrime, which is usually inflicted on a blockchain ecosystem. It is generally done by people who own more than 50% of the network’s mining rate.
How does it happen, though?
Well, let’s say you own around 51% of the nodes available in a blockchain environment. It, in turn, will enable you to have the power to alter the whole ecosystem. For example, you can –
- Prevent a new transaction from gaining confirmation.
- Perform a reverse transaction that was completed previously.
- Double-spend someone else’s coin without any barrier.
But, you can avoid this issue by choosing the right broker and availing their assistance to get to the right ecosystem. Check out this article on stash vs betterment to know more about it.
A Technical Overview Of The Proceeding Of A 51% Attack
A blockchain ecosystem, in essence, is a distributed ledger, almost like a database. Hence, it’s capable of recording information and transactions as they happen within the environment.
Almost everything in a blockchain network is secured through a cryptographic procedure. So, even if you try your best, you won’t be able to change anything no matter what.
However, this rule bends a little when it comes to the 51% attack.
As stated before, it’s done by people who’re carrying more than 50% of the hashing power of the ecosystem. It’s the computing element that solves the cryptographic processes.
Therefore, as the group of people holds more than 50% of the hashing power, they can easily create an altered version of the blockchain system. And, it’ll be theoretically accepted by the network as the group will own most of the same.
Hence, now, they can change the historical blocks of the same whenever they want. However, if the transaction was made quite a while back, it might be difficult for you to change it. And, in that case, the 51% attack will be nullified.
51% Attack – The Likelihood Of It
Unleashing a 51% attack, unlike how it seems, isn’t easy at all. For example, as a blockchain network grows, it’ll start hard-coding all the transactions within the software program.
Thus, it’ll be quite difficult for people to erase the available data and change it. And, that’s not all, though. A 51% attack can also be –
- Incredibly expensive, as the attacker has to expend a massive amount of money to get the computing power required for the job.
- As the attacker isn’t acting in a normal or projected manner, they also won’t be able to get the mining rewards from here. So, that’s a bummer.
Also, the older a blockchain network is, the more difficult it’ll be for you to change it, thanks to the hard-coding system. Hence, if you’re currently operating in an older ecosystem, like a BTC or Ethereum-based one, the risk of such an attack will be highly unlikely.
Examples Of A 51% Attack
The 51% attacks are more common in the newly-created blockchain ecosystems. Thus, in this section, we’ll focus on two attacks that happened on popular platforms, like
Bitcoin Gold (2018)
Bitcoin Gold, a form of Crypto based on Bitcoin, suffered a massive attack that led to around 18 million USD in theft. It happened in 2018, during the earliest year of Cryptocurrency.
Ethereum Classic (2019)
Based on the coveted Ethereum blockchain platform, Ethereum Classic experienced a huge 51% attack in 2019. It led to a loss of around USD 1.1 million.
Final Say
Although it’s not easy to perform, a 51% attack can massively affect a blockchain ecosystem. Therefore, it’ll be best for you if you could stay away from a newly-created environment.
We’ll also ask you to work with proper security-related aspects and be careful about it all. Or else, it might be impossible for you to avoid such an affecting attack as a whole.